Browse containerised applications, install them into the Data Vault, and run them against data that never leaves the organisation's environment. Developers publish. Organisations deploy. Data stays put.
The reverse data model means applications run inside the vault. The organisation browses the marketplace, selects what it needs, and deploys with one click. The data never moves. The application logic runs against it in place.
This is IP protection by architecture, not by contract. Developers never see the data. Organisations never expose the data. The application meets the data inside a sovereign environment.
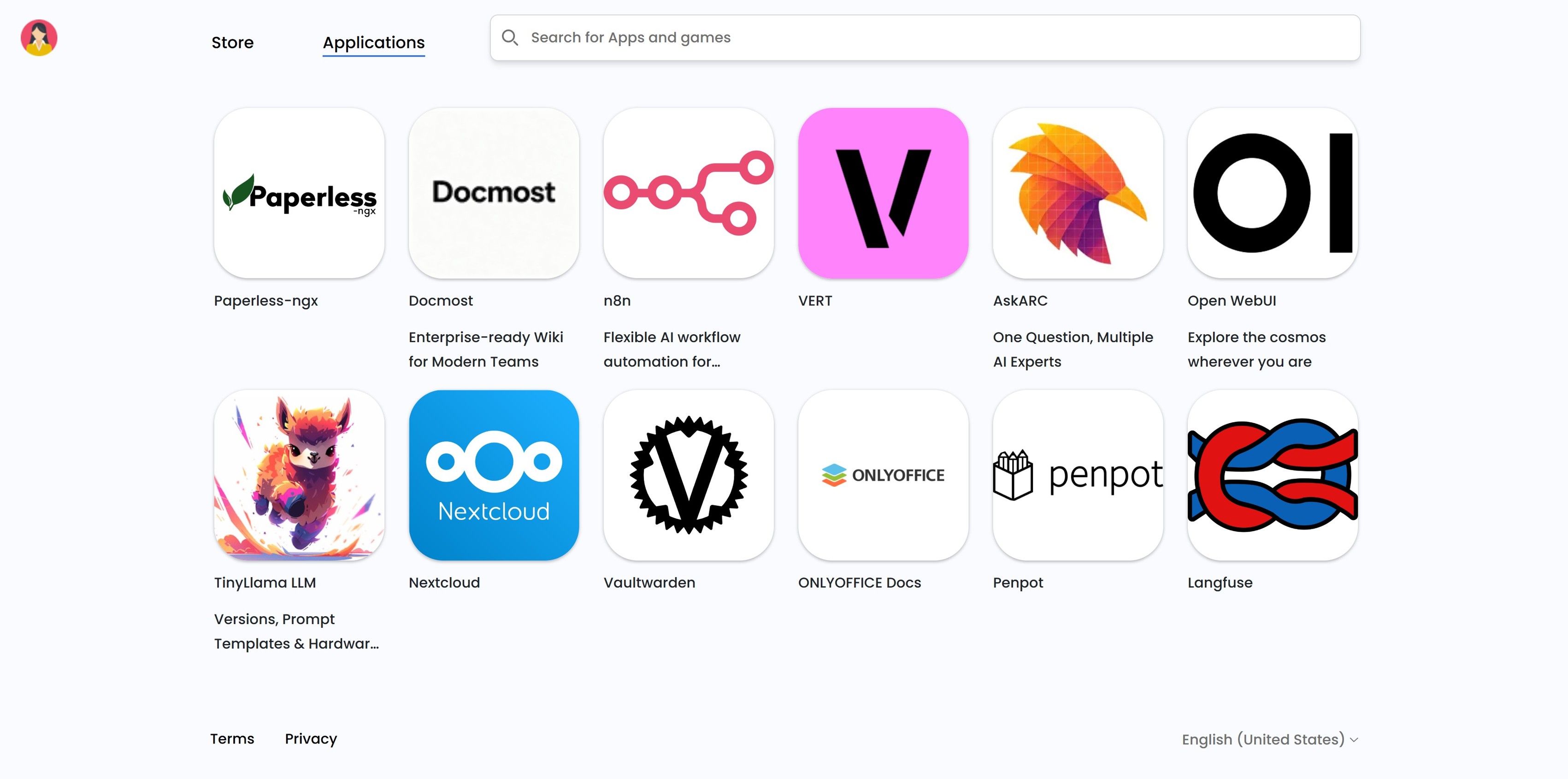
Categorised catalogue, one-click install, integrated into the Data Vault dashboard.
Three ways the marketplace works, for the organisation, for developers, and for everyone who needs something that is not yet on the shelf.
Every application in the catalogue is available to deploy into the Data Vault. No separate contracts, no data transfers, no copy operations. Select and install.
Developers publish applications to the marketplace through the developer dashboard. Once approved, they are available to every organisation on the platform.
Missing an application the organisation needs. Submit a request. The Bubl team reviews it and works with a developer partner to bring it to the marketplace.
Search and filter every application currently available in the Bubl Cloud marketplace.
Inside the Data Vault. Each application is containerised and deployed into the organisation's encrypted environment. Data never leaves the vault.
A mix of open-source projects, third-party developers who publish through the developer dashboard, and applications commissioned by Bubl Cloud and its partners.
Yes. Administrators control which applications from the catalogue are visible and installable for their users. The default is open, but it can be scoped to a curated subset.
Through the contact form or directly via the Bubl team. The team reviews the request, checks whether an open-source equivalent exists, and works with a developer partner where needed.
The application runs inside the vault. The organisation uses the interface. Developers never see the data, and organisations never see the source code unless the developer chooses to open it. Protection is enforced by architecture.
For most applications in the catalogue, yes. Some applications with advanced configuration options require a short setup wizard. Everything happens inside the Data Vault dashboard.